Trusted vulnerability scanswithout the hassle
Scan your websites, servers, networks, and APIs.
View dashboards, get threat alerts, and generate audit-ready reports.
OUR CUSTOMERS
Preferred by teams who take cybersecurity seriously
What we do
HostedScan is simple and effective. Run a wide set of industry-leading tools to uncover vulnerabilities and secure your company.
PROVEN TOOLS
Level up your company's cybersecurity
Meet compliance requirements
Vulnerability scanning is essential for your compliance with SOC 2, ISO 27001, cyber insurance, and more
Reduce liability
With regulations such as GDPR and CCPA, failure to maintain reasonable security procedures is grounds for lawsuits and fines.
Mitigate security vulnerabilities
Identify CVEs and OWASP Top 10 issues in your systems. Prioritize remediation using industry-standard threat classifications.
Detect misconfigurations
Many breaches and hacks happen not through highly sophisticated attacks, but by exploiting simple misconfigurations and human error.
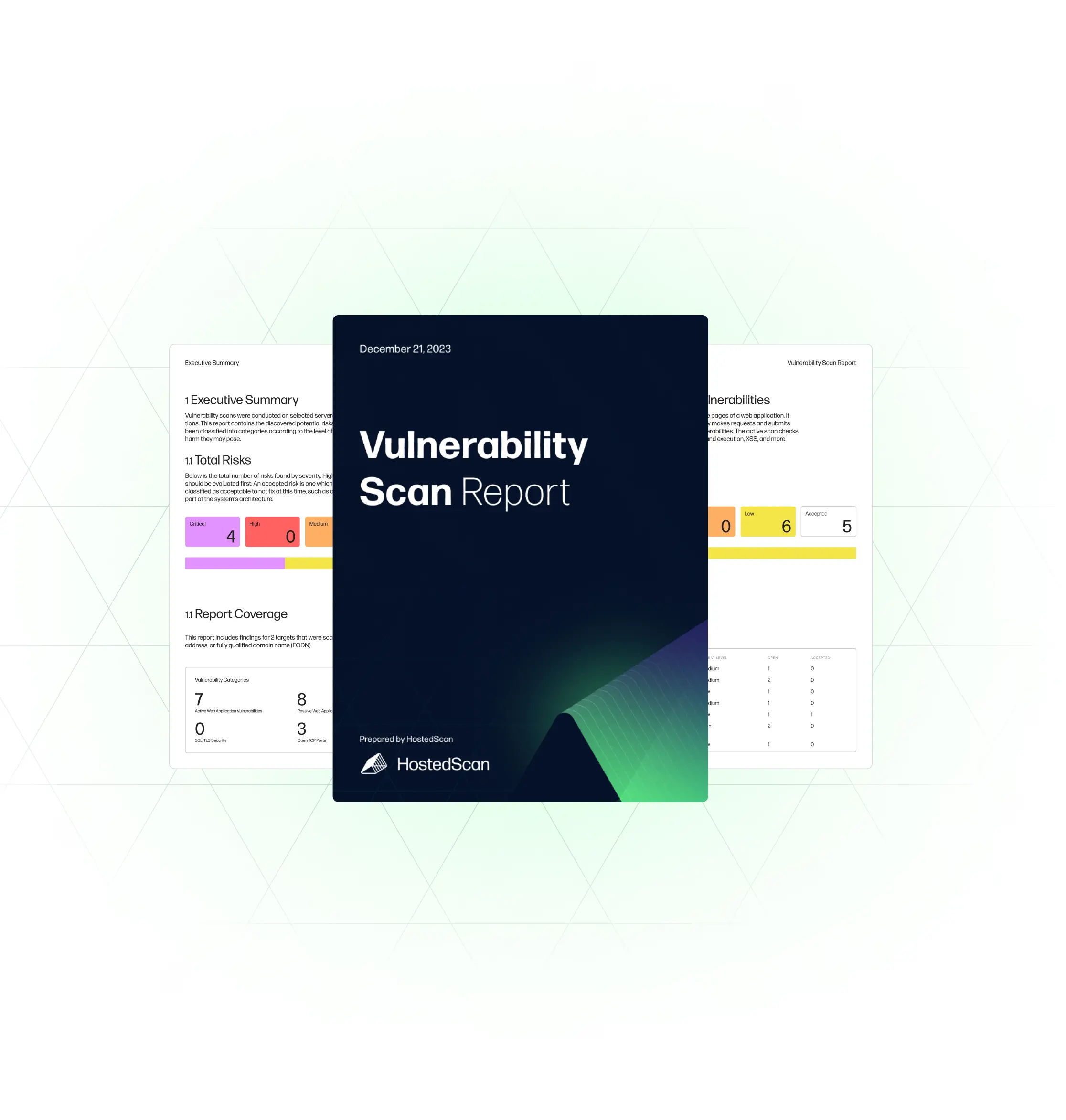
CUSTOM REPORTING ENGINE
Comprehensive reports, that always look good
Generate polished, branded reports for your executives, clients, or auditors
Communicate vulnerability risks
Get an executive PDF to share. See at a glance the vulnerabilities detected across all your targets or dive into each target, prioritized by risk level.
Export for your business intelligence
Use our built in reporting or export as CSV, JSON and XML to take into your BI tools, for full customisation.
White label reporting
Prepare custom white label reports for your clients. Make your logo and brand exclusive on the report.
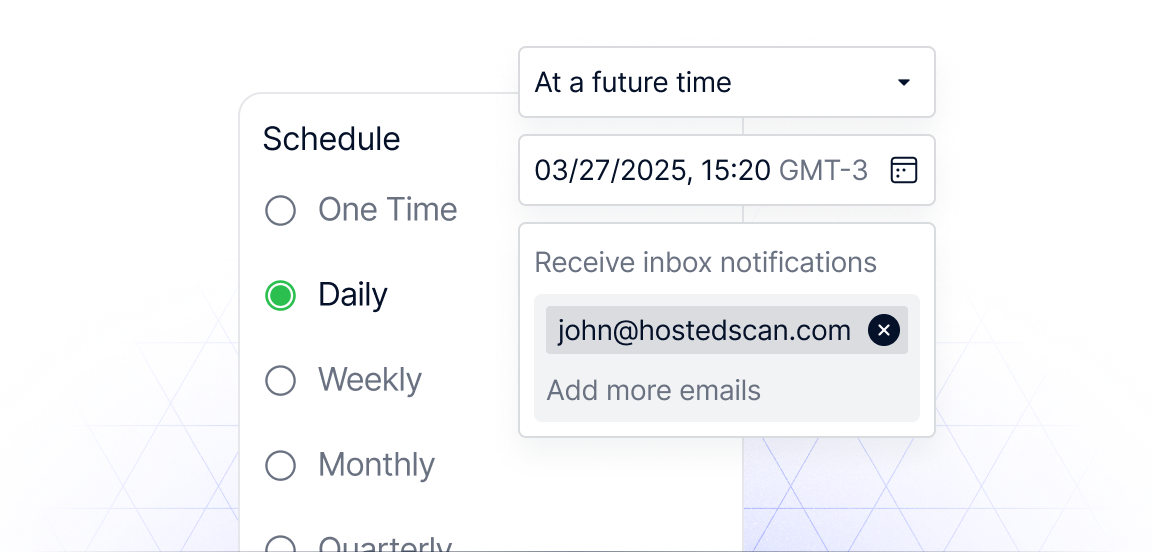
Scheduling & notifications
Always-on protection, without the noise
When a new port is open, or a new risk is detected, automatically alert your team. Cut out the noise. Only new or unexpected risks are alerted.
Get startedREST API & WEBHOOKS
Developer APIs + Webhooks
Add targets, run scans, and get results programmatically. Embed HostedScan into your own products and services.
Read our API DocsFROM OUR CUSTOMERS
What our customers are saying
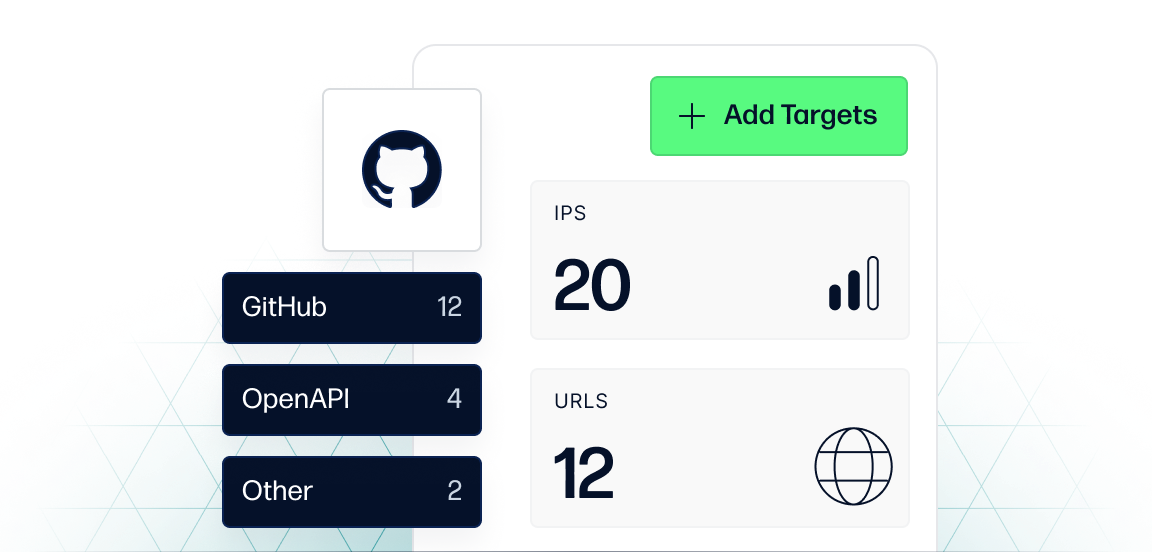
YOUR ENTIRE ATTACK SURFACE
Leverage the industry's most-trusted security tools
HostedScan includes a comprehensive suite of industry-trusted vulnerability scanners.
The advantage? Leverage the work of thousands of contributors and industry veterans behind these trusted tools, all in a package built for businesses like yours.
OpenVAS
Find insecure software and scan for Common Vulnerabilities and Exposures (CVEs).
Learn about OpenVASNmap
Ensure your firewall and network are configured correctly with nothing unintentionally exposed.
Learn about NmapOWASP ZAP
Focus on your web application, and detects front-end and API vulnerabilities.
Learn about OWASP ZapSslyze
Analyzes your SSL/TLS configuration and detects bad certificates, weak ciphers etc.
Learn about SslyzeGithub Dependabot
Manage Dependabot vulnerabilities in one place.
Get startedOpenAPI (Swagger)
Scan your APIs for potential weaknesses and security risks.
How to scan your APISnyk
Centralize risks for your containers alongside your scans.
Get startedImport via API
Bring in any third party risk source using our API.
Read our API DocsKNOWLEDGE HUB
Dive into HostedScan's Knowledge Hub
View allBecome a more secure company today
HostedScan enables companies to meet compliance and security goals.